-
What Is Incident Response?
- Why Is Incident Response Important?
- Types of Cybersecurity Incidents
- What Is the Incident Response Lifecycle?
- What Is an Incident Response Plan?
- What Is Digital Forensics and Incident Response?
- Incident Response Frameworks and Phases
- Incident Response Teams
- Incident Response Tools and Technology
- Incident Response Services
- Incident Response FAQs
-
What is Cloud Incident Response?
- Cloud Incident Response (IR) Explained
- Why Cloud IR Differs from Traditional IR
- The Cloud Incident Response Lifecycle
- SOC IR vs. Cloud IR
- Best Practices for Cloud Incident Response
- Cloud Incident Response Frameworks and Standards
- The Role of Cloud-Native Security Tools
- Future Trends in Cloud Incident Response
- Key Challenges in Cloud Incident Response
- Solutions to Overcome Cloud IR Barriers
- Cloud Incident Response FAQs
- What Is an Incident Response Plan (IRP)?
- What is Cyber Incident Reporting?
- What is an Incident Response Playbook?
-
What is the Role of EDR in Digital Forensics and Incident Response (DFIR)?
- Digital Forensics vs. Incident Response
- Exploring Fundamentals of EDR Incident Response and Forensics
- The Core Features of EDR Solutions
- The Intersection of EDR and Incident Response
- Enhancing Forensic Capabilities with EDR
- Integrating EDR into Your Cybersecurity Strategy
- DFIR vs. EDR
- CSIRT vs. Digital Forensics
- Challenges with EDR in Incident Response and Forensics
- Case Study: Impact of EDR in Real-World Scenarios
- The Role of EDR in Incident Response and Forensics FAQs
- What Is an Incident Response Team?
- What is an Incident Response Plan Template?
What is Digital Forensics and Incident Response (DFIR)?
Digital Forensics and Incident Response (DFIR) is a critical cybersecurity practice that combines two key areas: digital forensics and incident response.
Digital forensics focuses on collecting and analyzing digital evidence after a security incident, while incident response is about detecting, containing, and recovering from threats in real-time. Together, DFIR helps organizations minimize damage, understand how an incident occurred, and strengthen defenses to prevent future attacks.
AI-Driven Cybersecurity: The Future of Threat Detection & Response
DFIR: A Symbiotic Relationship
DFIR stands for Digital Forensics and Incident Response. This specialized area involves gathering and analyzing digital evidence to understand the details of a cyber incident, ensuring legal compliance, and preparing adequate response strategies. This dual focus makes DFIR critical for both proactive and reactive cybersecurity measures.
DFIR is more than the sum of its parts; the integration of digital forensics and strategic incident response allows for a comprehensive approach to cybersecurity. Digital forensics provides the necessary insights and evidence that inform and enhance the incident response process. Together, these disciplines enable organizations to manage cyber threats and data breaches better.
The Role of Digital Forensics
Digital forensics is the process of collecting, preserving, and analyzing digital evidence from various digital devices, including computers, mobile phones, and networks. In cybersecurity, digital forensics plays a crucial role in determining how a security breach occurred, potentially identifying the attackers, and ensuring the integrity of evidence for legal proceedings.
Key Functions of Digital Forensics
NIST (National Institute of Standards and Technology) outlines the digital forensics process in four major steps, based on their guide NIST SP 800-86: Guide to Integrating Forensic Techniques into Incident Response.
They are specified as follows:
| Step | Description |
| 1. Collection | Identify, label, record, and acquire data from relevant sources while preserving its integrity. This includes hard drives, memory, network logs, mobile devices, cloud systems, and more. |
| 2. Examination | Use forensic tools and techniques to identify and extract relevant pieces of information from the collected data. This may include filtering, recovering deleted files, or decoding artifacts. |
| 3. Analysis | Interpret the extracted data to reconstruct events, understand the nature of the incident, identify root causes, and establish timelines. This step connects the dots between the evidence. |
| 4. Reporting | Document the findings clearly, explaining what was discovered, how it was analyzed, and what conclusions were reached. The report should be thorough enough to support legal, regulatory, or internal actions. |
Everyday Use Cases include:
- Investigating data breaches or ransomware attacks
- Tracing insider threats or employee misconduct
- Supporting legal or regulatory investigations
- Identifying the root cause of system compromises
What is Digital Evidence in Cybersecurity?
Digital evidence includes any information of probative value that is stored or transmitted in digital form, often used in cybercrime investigations. It can range from logs of network activity to recovered deleted files on a hard drive. Proper handling of digital evidence is paramount to its admissibility in court.
The Role and Importance of Incident Response
Incident response refers to the structured methodology employed to address and manage the aftermath of a security breach or cyberattack. Its goal is to handle the situation in a way that limits damage and reduces recovery time and costs. An effective incident response requires a well-defined process for detecting, responding to, and recovering from security incidents.
Key Components of Incident Response
DFIR provides the structure security teams need to minimize damage, recover quickly, and strengthen defenses against future cyberattacks.
Here are the six essential steps of the DFIR process:
- Preparation: Develop policies, tools, and team roles before incidents occur. This includes setting up secure baselines, maintaining logs, and conducting regular training.
- Identification: Detect and confirm the incident. Use threat intelligence, monitoring tools, and alerts to pinpoint abnormal activity and determine the scope and type of attack.
- Containment: Limit the spread of the threat—triage systems to isolate affected assets while preserving forensic evidence for further investigation.
- Eradication: Remove malware, unauthorized access, or compromised components from the environment. Patch vulnerabilities and restore systems to a secure state.
- Recovery: Safely return to normal operations. Monitor restored systems for any residual threats and validate that all vulnerabilities have been addressed.
- Lessons Learned: Conduct a post-incident review to improve response processes. Update documentation, improve detection methods, and close security gaps revealed during the incident.
This repeatable, closed-loop process ensures continuous improvement and builds long-term resilience against evolving threats.
What is the Difference Between DFIR and SOC?
The Security Operations Center (SOC) and DFIR play distinct roles within cybersecurity.
SOCs are teams dedicated to monitoring and responding to security incidents in real-time. While SOCs focus on detection and alerting, DFIR deals with investigating and responding to identified incidents. Together, these functions enhance an organization's overall security posture.
The Role of EDR in DFIR
Endpoint Detection and Response (EDR) solutions are tools that provide real-time monitoring and threat detection at endpoints. DFIR, meanwhile, encompasses a broader scope, incorporating digital forensics to understand incident specifics and executing complete incident response cycles to remediate threats effectively.
Discover how EDR incident response and forensic solutions empower IT professionals: What is the Role of EDR in DFIR?
Top 5 DFIR Tools
Effective DFIR relies on precision, and that starts with deploying proven tools for endpoint monitoring, forensic acquisition, memory analysis, and incident management. A strong DFIR toolkit should cover endpoint visibility, network insights, threat intelligence, forensic investigation, and response automation, giving teams everything they need to detect, contain, and recover from attacks quickly.
The top five tools every security team should have are as follows:
- EDR Platform: Provides real-time visibility into endpoint activities, detects threats, and supports detailed forensic investigations across devices.
- Network Traffic Analysis Tool: Captures and analyzes network communications to uncover anomalies such as lateral movement, command-and-control traffic, or data exfiltration.
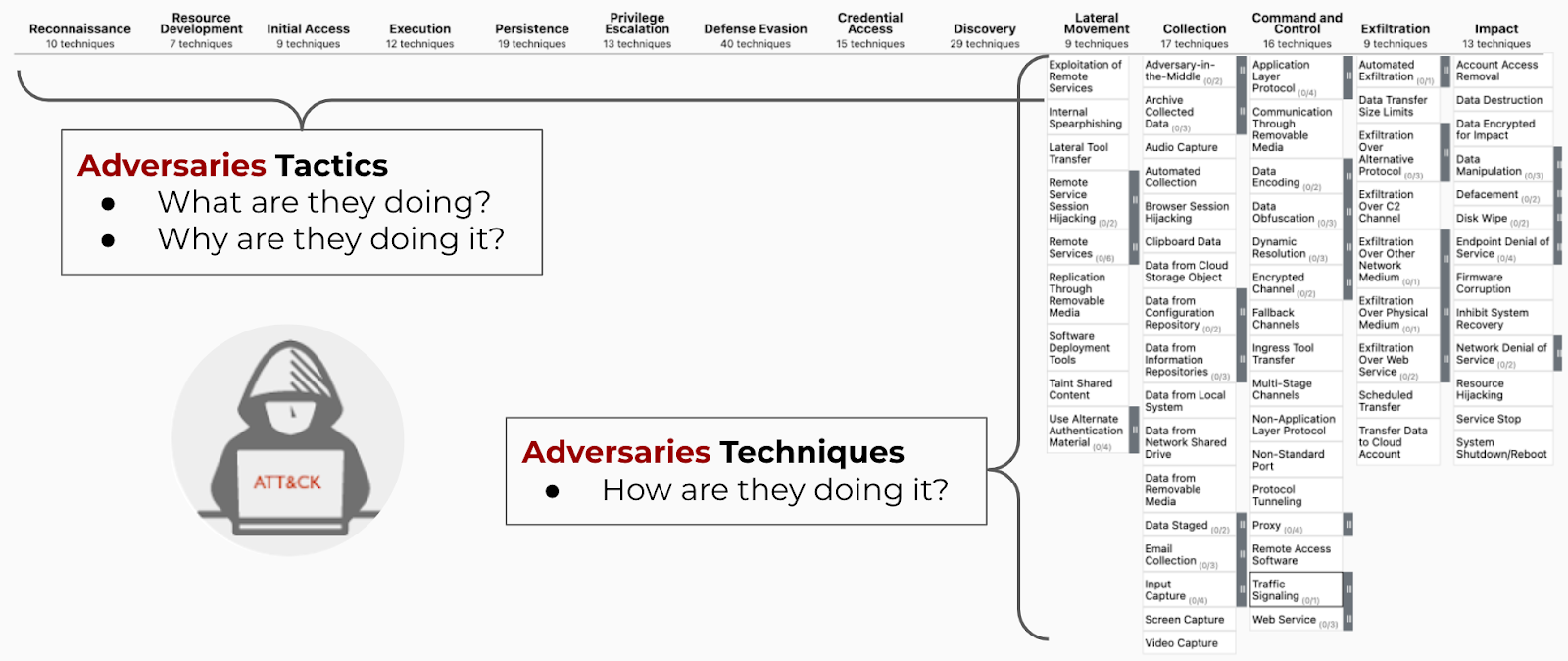
- Threat Intelligence Platform (TIP): Aggregates global threat data to enrich investigations, helping analysts understand attacker tactics, techniques, and indicators of compromise.
- Forensic Collection and Analysis Tool: Gathers memory dumps, disk images, and file system metadata to enable deep forensic examinations without altering the original evidence.
- Security Orchestration, Automation, and Response (SOAR) Platform: Automates incident response workflows, centralizes case management, coordinates tool actions, and improves investigation speed and consistency.
DFIR Team Roles and Responsibilities
In a DFIR operation, digital forensic investigators are tasked with recovering and examining digital evidence, while incident response teams are responsible for implementing strategies to mitigate the impact of the breach and prevent future incidents. Collaboration between these teams ensures a resilient defense against cyberthreats.
Skills Required for DFIR Professionals
Professionals interested in pursuing a career in DFIR should possess a blend of technical and analytical skills:
- Strong understanding of operating systems and file systems
- Knowledge of network security and protocols
- Experience with forensic tools and methodologies
- Ability to analyze and interpret digital evidence
- Proficiency in scripting or programming languages
DFIR Challenges
As computer systems have evolved, so too have the challenges involved in DFIR. There are several key obstacles digital forensics and incident response experts face today. These challenges call for DFIR experts to help support growing alerts and complex datasets and take a unique and flexible approach to threat hunting within modern, ever-evolving systems:
- Slow Detection — Threats often go unnoticed for weeks or months.
- Evidence Preservation Risks — Poor handling can destroy critical data.
- Cross-Team Coordination Issues — Response delays due to miscommunication.
- Advanced Threat Techniques — Attackers use stealthy, complex methods.
- Overwhelming Data Volumes — Massive logs and traffic complicate investigations.
- Skills and Tools Gaps — Specialized expertise and software are often missing.
- Chain of Custody Challenges — Mishandled evidence can lose legal value.
- Balancing Speed and Accuracy — Rushing or delaying worsens outcomes.
- Changing Compliance Rules — Regulatory demands are evolving.
- Attacker Obfuscation — Hackers hide their tracks with encryption and misdirection.
Digital Forensics and Incident Response Best Practices
In today’s high-stakes threat landscape, following DFIR best practices are essential for minimizing business disruption, protecting digital assets, and ensuring a fast, coordinated response to cyber incidents.
| Best Practice | Why It Matters |
| Prepare Before an Incident Happens | Build an incident response plan, assemble a DFIR team, and run regular tabletop exercises. Being ready reduces response time and chaos. |
| Establish Clear Communication Channels | Define how internal teams, legal, executives, and external partners (like law enforcement) will communicate during incidents. |
| Collect and Preserve Evidence Early | Capture volatile data (such as memory and network traffic) and secure system images before containment to maintain forensic integrity. |
| Prioritize Containment Over Full Eradication | Quickly isolate the affected systems to prevent the spread, while carefully preserving the data for investigation. |
| Document Everything | Keep detailed logs of actions taken, timelines, communications, and findings. Good documentation is vital for audits, legal cases, and lessons learned. |
| Use the Right Tools for Forensics | Deploy trusted forensic tools and platforms to gather, analyze, and store evidence securely and reliably. |
| Focus on Root Cause Analysis | Don't just clean up the symptoms; address the root cause. Investigate thoroughly to understand how the attacker gained entry and how to close that entry point. |
| Automate Where Possible | Use automation for incident detection, evidence collection, and response orchestration to speed up and standardize DFIR processes. |
| Implement Continuous Monitoring | Maintain visibility across endpoints, networks, and cloud environments to spot unusual behavior early. |
| Conduct Post-Incident Reviews | After recovery, meet to discuss what worked, what didn’t, and how to improve your DFIR plan for the future. Update policies and training based on findings. |
“The 2025 Unit 42 Global Incident Response Report reveals a shifting threat landscape marked by faster, more complex attacks.”— Unit 42 Global Incident Response Report 2025
Future Trends in DFIR
The future of DFIR will be faster, wiser, more cloud native, and more critical to managing cyber risk across complex digital ecosystems.
- AI-Driven Investigations: Machine learning will automate evidence analysis, timeline creation, and anomaly detection, enhancing speed and scalability.
- Cloud and SaaS Forensics: DFIR will evolve to capture and analyze evidence across cloud platforms, containers, and SaaS ecosystems.
- Proactive Threat Hunting Integration: DFIR will shift left, blending threat hunting, behavioral analytics, and continuous monitoring into daily operations.
- Forensics for IoT and Operational Technology (OT): Investigations will expand to include smart devices and critical infrastructure, utilizing new tools and methods.
- SOAR-Integrated Forensic Automation: Automated playbooks will collect and correlate forensic artifacts, dramatically reducing response time.
